
Many of us love free public Wi-Fi, and many merchants are eager to provide free Wi-Fi as one of their value-add services. But we know public Wi-Fi can be dangerous. The freely accessible unencrypted network is easy for the bad guys to watch our Internet activities. It doesn’t help that some merchants cannot be bothered about security either.
I single out StarBucks, as an example, though there are certainly many others like them, because I use their Wi-Fi regularly, and I’ve complained about their Wi-Fi security previously. They’ve now changed provider, to MyRepublic, and the problematic issue is back again.
The situation is like this. Once upon a time, StarBucks offered free Wi-Fi that was simple and straight-forward to use. Just connect to the Wi-Fi SSID and start surfing the Internet, there’s no need to provide any information to them. If you know the risks of public Wi-Fi, then just deal with it in whatever way you think fit. If you don’t, well, StarBucks didn’t make things worse.
One day, their then provider Y5Zone decided that it would be really cool to ask for some information. They did so over an unencrypted web page. You must provide information, including some personal information, before you could use the network. I was really annoyed.
I was not just angry that they make users divulge personal information over an unencrypted channel, but that their own FAQ falsely promised that their service was secure. This is their claim:
Y5ZONE hotspot is secure, and however secure the system is, all data is sent as clear text between the user’s computer and the wireless router, unless the user is connecting via a secure protocol (https/ssl, secure pop3, etc.). Generally, this is how the Internet works. However, you should not need to worry as we have taken the necessary steps to ensure the service is secure. You may read our Privacy Policy for further details.
What steps did they take? That’s something I cannot comprehend. They have forced users to submit personal information over an unencrypted web connection, and yet have the audacity to assure users they’ve taken the necessary steps to ensure security. That’s just a blatant lie.
So I complained. I wrote to Y5Zone. After beating around the bush initially, they eventually got HTTPS provisioned. Good.
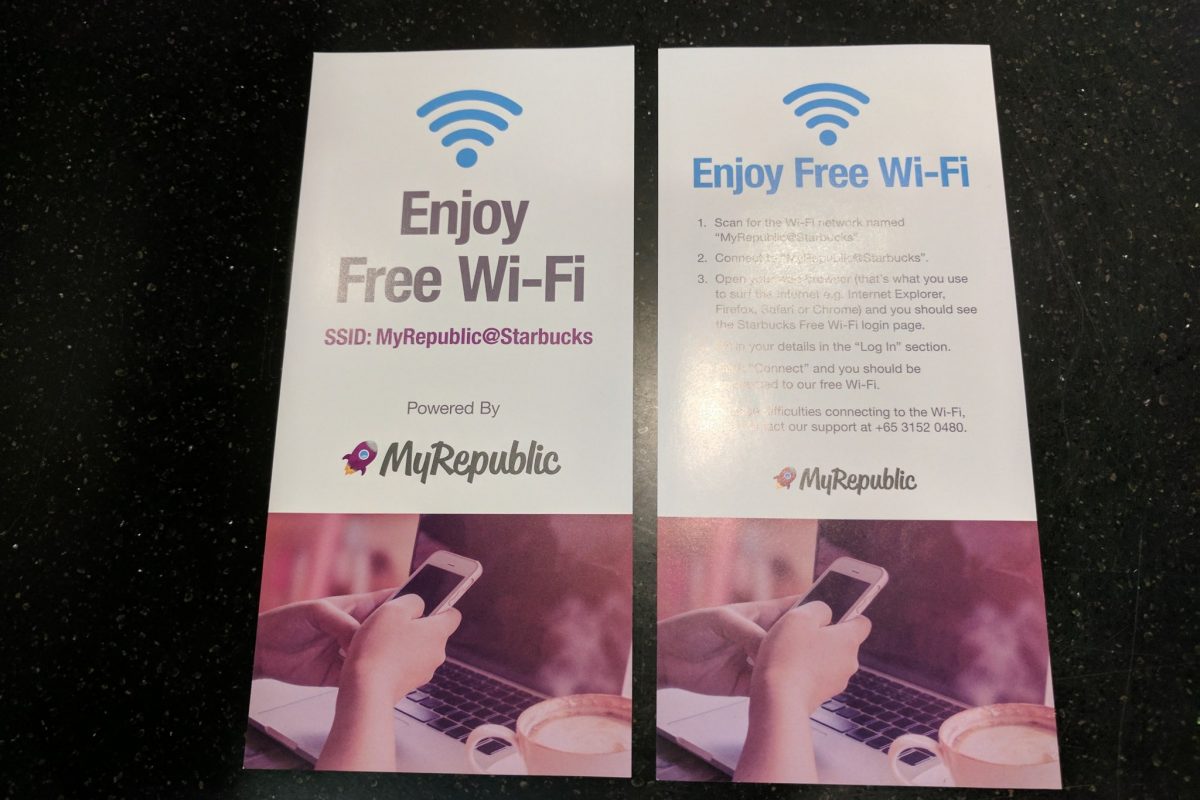
Except now I found that Starbucks uses another provider. Or perhaps some other outlets use a different provider. This other one is MyRepublic. They are back again with that unencrypted webpage asking for personal information before granting network access.
Perhaps the best way to deal with these companies is to simply shame them publicly.
In fact, I am shocked that MyRepublic, the company that so valiantly wants to become Singapore’s 4th telco and shake up the postpaid telco market, couldn’t even be bothered with basic security. Really? Asking for user information on a non-secure webpage, unencrypted, over free public Wi-Fi?
Apparently MyRepublic might not be directly responsible for the Wi-Fi captive portal themselves, as it seems they’ve partnered with D-Synergy. It seems they call themselves one of South-East Asia’s fastest growing *cough* *cough* Internet Security and Networking technology distributors.

Hey, how hard is it to just secure the captive portal website? SSL certificates too expensive? Can’t be, there are free ones available (e.g. Let’s Encrypt). Perhaps it’s too complicated for them to handle?
These companies must be reminded that their disinterest with security isn’t something that they can just let slide. It doesn’t mean that just because most users don’t know, or don’t know enough to care, that they can just chuck security away.
It’s actually illegal. If they collect personal information, they are required by law to protect that personal information. The Personal Data Protection Act (PDPA) places on organisations an obligation to protect personal information.
Technically, they have flouted the law by so carelessly collecting information in the manner they do.
I’ve written to Starbucks, MyRepublic and D-Synergy for their comments, and will see what they have to say.
As mentioned earlier, they are by no means the only ones. I had observed that KFC does a similar thing when I casually checked out their Wi-Fi when I was nearby. McDonald’s Wi-Fi too, is a similar story. I’m pretty sure there’s a long, long, list of such public Wi-Fi. I’ve tried before, and for something so simple, it takes far too much effort to try to convince the providers that something needs to be done.
It might be far easier to shame them, and get the public to pressure them to change.
ps: While preparing the above post, I observed that Wireless@SG is, erm, perhaps just as bad. In fact, they provide an illusion of security on the surface, but the execution is completely a facade to misdirect people. I’ll talk about that another time. IMDA themselves need a wakeup call.
Update (2016-12-03): MyRepublic responded to my email. They explained that the service wasn’t launched yet, and that they were only testing. SSL is planned when the service is launched on 1st December. I’ve since checked back and confirmed SSL is used. Testing a service i public in such insecure manner is bad, of course, and they admitted as much. What puzzles me is that if the service was only in testing, why were leaflets already distributed at Starbucks outlets to announce the service? The leaflet had not said that 1st December was the official availability date. Also, you might notice that the SSL certificate used by MyRepublic appears to be a free COMODO certificate that’s valid for only three months.
Hi Zit Seng,
Maybe you can refer them here: http://statutes.agc.gov.sg/aol/search/display/view.w3p;ident=ec593ff6-7aa0-48ee-9e92-96755c2804fb;page=0;query=DocId%3Aea8b8b45-51b8-48cf-83bf-81d01478e50b%20Depth%3A0%20Status%3Ainforce;rec=0#pr11-he-.
Hey Zit Seng,
Someone shared your post to me. I was curious myself, so i went to test McD. Not sure when you tested, but McD is on https. Keep up the awesome posts!
Regards,
John