
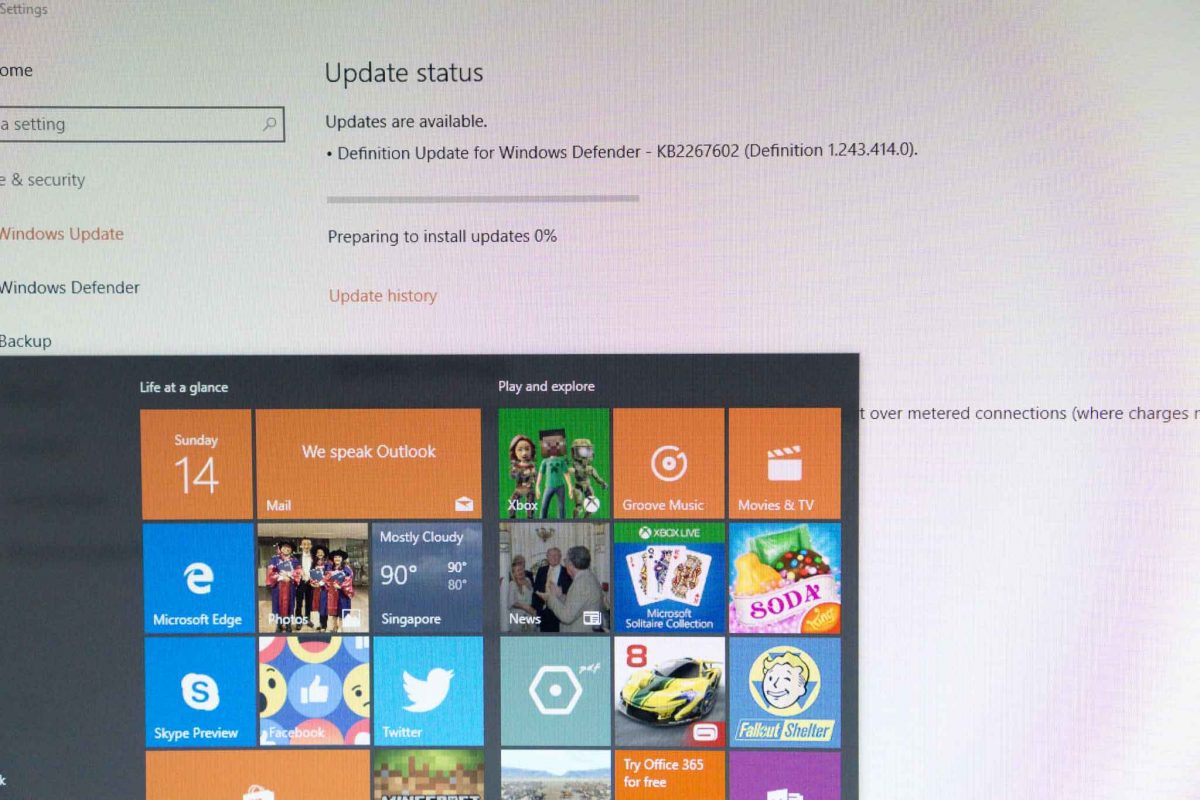
It’s been a really busy weekend. For me, partly because there was some fallout from the revelation of the cyberattack on NUS. Then, there’s the WannaCry ransomware outbreak. I decided to check on the Wife’s PC at home, and found to my horror that automatic patches have been failing for months. Why does Windows keep silent about failed updates?
I’ll save the story on the Windows update for another post. There’s something more urgent going on with WannaCry. Anyone who is at least reasonably tech-savvy and keeps abreast with developing tech news will know by now.
On Friday, 12 May 2017, a large-scale cyber-attack was launched targeting Microsoft Windows PCs. It infected too many computers in too many countries, encrypting their contents, and demanded ransom payments in bitcoins. It’s a ransomware, and it became known as WannaCry, and a few other variant names like WannaCrypt, WannaCryptOr, Wanna Decryptor, and even Wcry.
WannaCry exploited a vulnerability in Microsoft Windows, but on versions of Windows still actively supported by Microsoft, a patch to address that vulnerability was issued on 14 March 2017. Yet, clearly, nearly two months later, many Windows computers remain unpatched.
In an interesting turn of events, someone accidentally discovered a kill-switch. It’s a feature that allows someone, presumably the ransomware originator, to stop or slow the spread of the malware, if at some future time it was desired. So the kill switch was flipped. It only costs all of US$10.69, to buy the domain name required to activate the switch.
Still, you should patch your vulnerable Windows if you haven’t done so. I hope no one thought they should just chill out the rest of the weekend.
Now, they can’t. WannaCry 2.0 is now upon us. Its new feature? There’s no kill-switch.
Fix your Windows PC now.
Understand that WannaCry can spread and infect your PC without needing any action on your part. While the initial needs to arrive via an emailed web link or attachment, the infected PC can then reach out laterally to infect other computers on the same network. The malware exploits a vulnerability in SMB, the file sharing protocol used in Microsoft Windows.
Fun fact. WannaCry is believed to have used an exploit developed by the U.S. National Security Agency (NSA).
To know positively if your Windows is suitably patched against the vulnerability exploited by WannaCry, check that:
- If you have Windows 10 Creators Update (version 1703), you’re fine.
- If you have Windows 10 Anniversary Update (version 1607), you need build 14393.953 or later.
- If you have Windows 10 Fall Update (1511), you need build 10586.839 or later.
- If you have Windows 10 RTM (1503), you need build 10240.17319 or later.
From your Windows 10 desktop, press the Windows key, type “winver” and press Enter. You’ll find your version and build number in the window that opens.
For other versions of Windows, Google around, you’ll find the answers.
If you’re not patched, you need to fix your Windows PC now.
View Comment Policy